Pagoda Blog

The Fate of Internet Privacy Protection and Your Personal Electronic Data
April 5, 2017
|
|
Have you ever thought about how much of your personal data is stored online? Once you start making a mental list of all the apps, accounts, and email servers that store everything from your birth date to your credit card number, you may start feeling a little queasy. Is all that data actually secure? Who has access to this personal information and what are they doing with it?
Before we dive into the risks of storing your personal data online, keep in mind that we are not advocating for you to remove yourself or your business from the online marketplace. For most of us, the internet is now a necessary component of our day-to-day existence. This means you can’t just abstain from conducting any kind of professional or personal business online because there’s a chance of identity theft or credit card fraud. That would be like refusing to drive because you might get in an accident, and living your life in fear of car accidents and identity theft is obviously not the answer.
In this post, we explore some of the risks of a fully connected world, our government’s current stance on protecting us, and our own personal role in exercising reasonable caution with our online data.
Should you travel with your smart phone?You may have seen the article on Medium that went viral earlier this year titled, I’ll never bring my phone on an international flight again. Neither should you. It sounds a bit dramatic, right? But of course it grabbed the attention of thousands of readers and now has everyone considering whether they should leave their most precious possession behind during international travel.
In case you missed it or need a quick refresher, the story goes like this:
Sidd Bikkannavar, a US-born NASA scientist, flew back to Houston, Texas from Santiago, Chile on January 30 of this year. At the airport in Texas, Bikkannavar was detained by Customs and Border Patrol agents who refused to release him unless he told them the password to unlock his phone. Even though Bikkannavar explained that his phone contained sensitive information on it for his employer, NASA, the agents still demanded the password. In order to be released and go home, he finally gave in.
You’re probably thinking, ‘Wait, how is this legal?” While this wouldn’t be legal if you were, say, walking down the street somewhere in America, it is legal to demand access to your electronics at the US border, even without probable cause.
This seems strange, right? Although the fourth and fifth amendment should protect you against this kind of privacy violation, they can’t protect you at the US border because it’s technically not the US.
Scarier still is that these Customs and Border Patrol agents could be using software that can download and permanently archive all your personal information, like photos, contacts, passwords, email and social media accounts, in just a few minutes.
So should you stay at home, refuse to use the internet, and sacrifice your career and social life for the sake of security? Of course not. Unless you’ve been dying for the right excuse to go entirely off the grid, and then by all means, go for it.
For the rest of us, let’s look at some slightly more practical options …
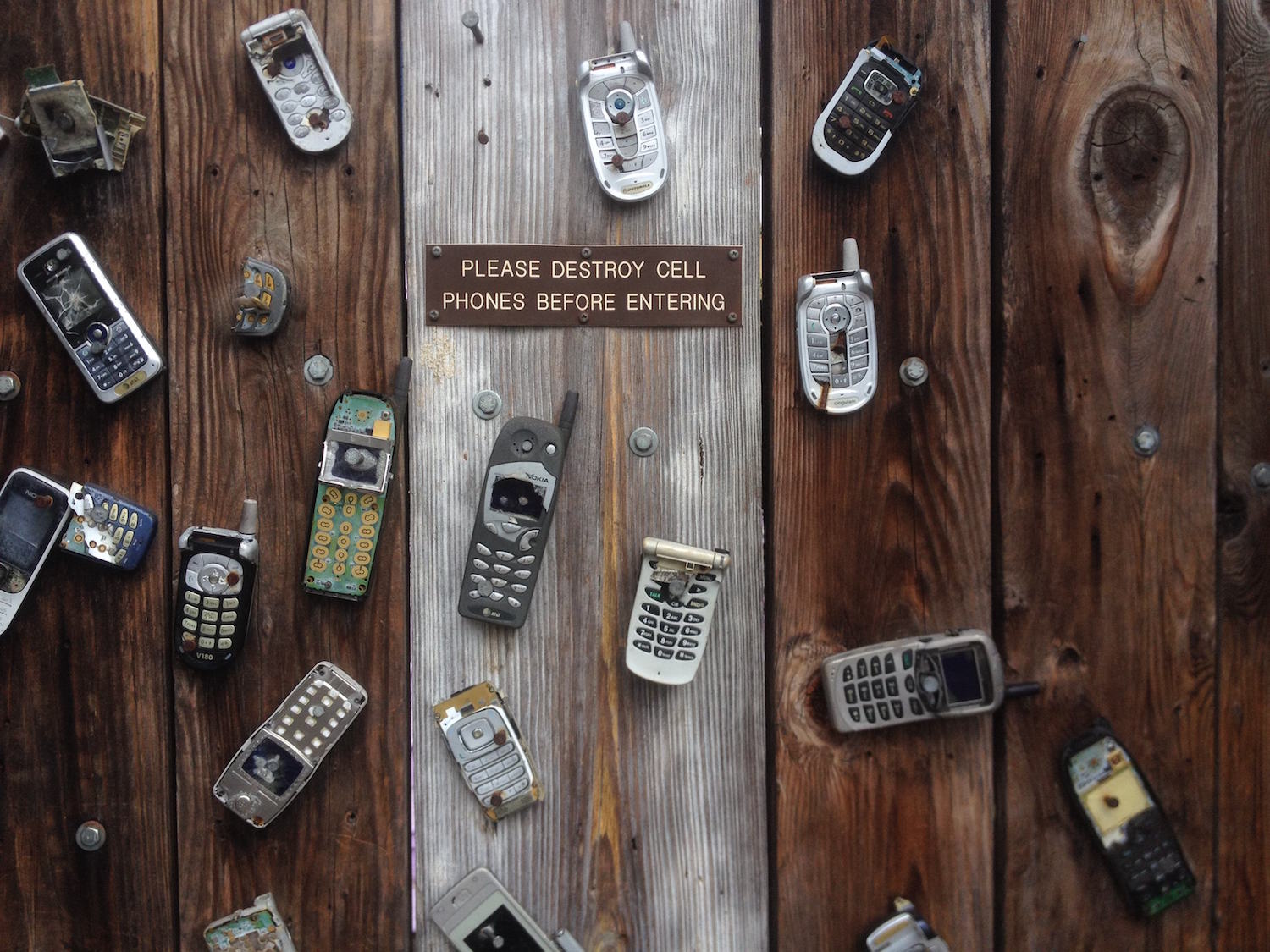
Take reasonable precautionsThe most obvious and practical solution is to leave your smartphone or laptop behind when you travel across borders. Purchase a burner for international trips or rent a phone and laptop once you reach your destination. If the thought of being separated from your smartphone for more than five minutes gives you cold sweats, then you do have another option. Before boarding your flight, reset your phone to its factory settings. All the data stored on Facebook, Instagram, your personal banking app, email accounts, etc. will now live safely in the cloud until you choose to re-access these accounts.
As an employer, you should also consider whether your employees are traveling with electronic devices that could jeopardize your business if they fell into the wrong hands. To keep your data secure, instate a policy that prevents employees from bringing phones or laptops containing sensitive company data on international trips. For business trips, offer to pay for the rental of a laptop and phone once employees arrive at their destination.
Online privacy at homeLast month, Congress voted to overturn the Internet privacy protections rule passed under the Obama administration in the last weeks of his presidency. The rule had yet to take effect but would have required Internet service providers (ISPs) to ask your permission before selling your personal data. This data includes your browsing history, geolocation, financial and health information, and more.
Although opponents of the new ruling argue that it essentially gives your personal information to the highest bidder, proponents counter that it will improve competition between online companies and stimulate the economy. This may be true, but at what cost? If it’s illegal to listen in on our phone conversations, then shouldn’t it also be illegal to track our activity online? It all depends on how we view the role of ISPs. Your ISP: Government regulated utility or profit-driven business?Your internet connection is usually provided by a phone company such as Comcast, Verizon, or AT&T. Those companies are utilities, required to follow certain government regulations, such as not allowing a third-party to wire-tap your phone without a warrant. As Manoush Zomorodi, host of WNYC’s tech podcast, Note to Self, points out, without the privacy protection rule, ISPs function as a for-profit business, uniquely positioned to profit off our personal data.
While it’s true that Google and Facebook collect and share our personal data without explicitly asking our permission, you can always choose to use a different internet browser or you can choose to close your Facebook account. It’s not nearly as easy to just switch ISPs and you can’t choose to opt-out altogether without giving up your access to internet.
So, should ISPs be regulated like all other utilities? Should they be required to ask our permission before they collect and sell our personal data? We don’t have a definitive answer, but these are the questions we all need to start asking ourselves before we lose our online privacy rights entirely.
If you need a little levity after hearing that your digital life is being tracked and put up for sale to the highest bidder, we have just the thing. Check out this satire of the whole situation from the New Yorker: Three Hundred and Seventy-Two Simple Ways to Protect Your Digital Life.
(We love the last tip: “The only way to guarantee that you won’t be compromised is to heed the remaining tips, which you can access for free by going to our Web site and typing in your Social Security number.” Hah!)
–––––––––––––––––––––––––––––––––––––––––––––––––––––––––– About Pagoda Technologies IT services Based in Santa Cruz, California, Pagoda Technologies provides trusted IT support to businesses and IT departments throughout Silicon Valley, the San Francisco Bay Area and across the globe. To learn how Pagoda Technologies can help your business, email us at support@pagoda-tech.com to schedule a complimentary IT consultation.
|
Return to Pagoda Blog Main Page |