Pagoda Blog

2016: The Year of Ransomware
July 7, 2016
|
|
On February 6th of this year, computers at a Hollywood Presbyterian Medical Center become infected with the .locky virus that shut down their communication capabilities. After a few days when the hospital had to resort to keeping records with pen and paper, they paid a ransom of 40 bitcoins (approximately $17,000) and regained access to their computer system.
This is happening all the time to hundreds of institutions all over the United States. Over 18 million dollars were paid to ransomware thieves between April 2014 and June 2015. More than 6 million detected ransomware attack attempts in Q4 2015 and 50% of all malware are now ransomware attacks.
Sometimes, like with the Hollywood Presbyterian Medical Center, institutions must pay the ransom to continue operations. Sometimes, like the lucky Los Angeles County Department of Health Services, institutions are able to isolate their infected devices and refuse to pay their captors. No cooperating with terrorists, even cyber ones. Industry experts are now agreeing that a staggering 93% of phishing emails now contain encryption ransomware, which means almost everyone is at risk.
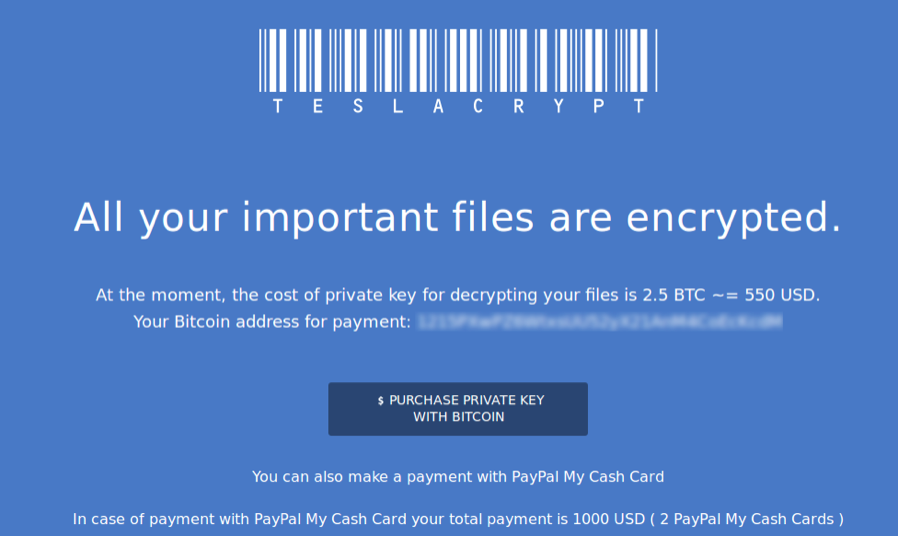
Image from www.fireeye.com
Hospitals, government agencies, school districts, police departments and more are getting hit with cyber criminals demands for bitcoin and the like. We have written a few articles in the past about cybercriminals and their prevalence in businesses, but it seems that social services and government positions are just as likely to be targets as small to medium sized businesses.
Within the last few months, security experts have discovered a ransomware program aimed at Apple device users embedded in Transmission, an app that allows users to Torrent movies and TV shows illegally. Apple upgraded its devices security software to block the virus, but approximately 6,500 computers were infected within the first 36 hours.
This virus is the .locky virus which you can read more about here, which locks important files in your computer, and changes the background of your computer to instructions, telling you to pay 1 bitcoin (approximately $410 USD) to the person holding your files hostage. The tell tale sign is that the extensions of the files held hostage change to ‘.locky’.
These attacks are insidious, because they are small enough to seem like a nuisance, something you can get over with and forget. However, with enough victims, the attackers can make large sums of money. $410 from one person isn’t a lot, $410 from 5,000 people is a different story.
Part of the problem is that people are more and more likely to entrust personal data and heirloom materials to their computers. You may not care about some work materials stored on your computer, but your family photos of a deceased relative? Those you will pay to have back.
As few as 25% of home computer users are estimated to regularly backup their data, that leaves 75% of people not backing up their files.
"People do not think rationally under time limits," he said. "The victim is subject to the anxiety of the ticking clock ... and the fear of regret if the data is lost forever." - James Scott, security expert
Another thing to consider on this chessboard of security experts and cyber criminals, is the backdoor the FBI asked Apple to create. After the San Bernardino attack in California, the FBI requested ‘backdoor access’ to the Apple devices belonging to the two attackers. Meaning anyone with the right set of keys could open Apple devices. It becomes not a question of ‘if’ someone could break into your phone, but ‘when’.
The FBI’s inability to stop these types of cyber attacks, is not limited to .locky type attacks. Last year, Assistant Special Agent in Charge of the Cyber and Counterintelligence Program in Boston, Joseph Bonavolonta, was quoted telling a gathering of cybersecurity experts, “To be honest, we often advise people just to pay the ransom.”
On an official level, the FBI asks targets of cyber attacks to notify the bureau. However this may or may not actually do anything to help victims. How can the FBI respond to hundreds, if not thousands of requests each day?
“The Bureau explains what the options are for businesses that are affected and how it's up to individual companies to decide for themselves the best way to proceed. That is, either revert to backup systems, contact a security professional or pay." - Spokesperson from the FBI Since the FBI cannot respond adequately to all cyber attacks, it is more important than ever for people to take their security into their own hands. It is necessary for small business owners, government agencies, law firms, hospitals, even schools to make sure that they have proper back ups, updated software, and trained employees who know how to respond to cyber attacks quickly. For a complete list of all recommended responses to a cyber attack on yourself or your business, please see the FBI’s official statement.
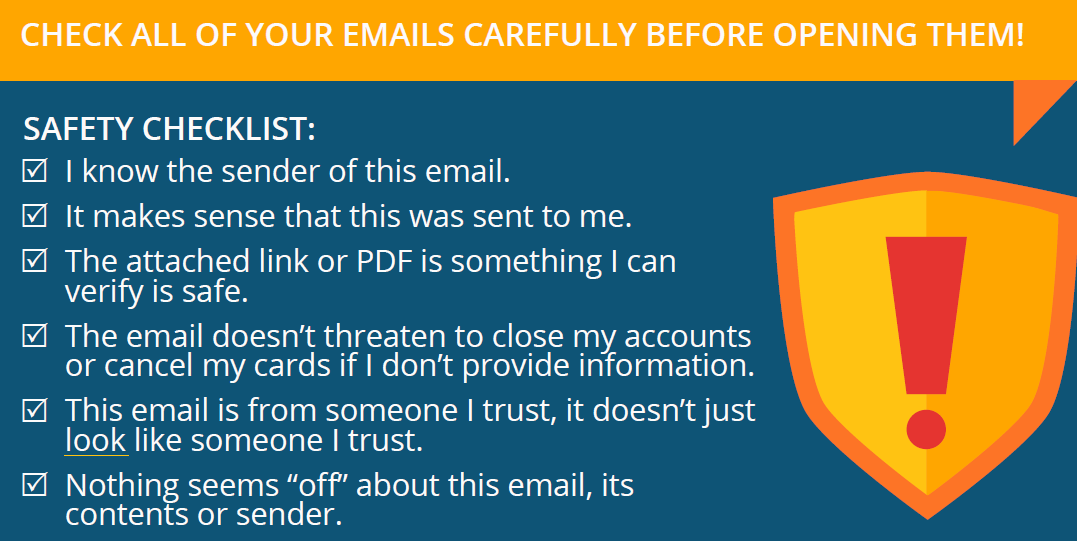
The chances are, if it looks to good to be true, it probably is. Close pop-ups as soon as you can and never click on anything that says, “You’re a winner!”. These are cheap tactics to get users to follow a rabbit hole and download a virus. When using your email, please refer to this checklist.
Image from solarwinds.com
If you or your company have been a victim of cyber attacks, please contact us at support@pagoda-tech.com for a free consultation.
–––––––––––––––––––––––––––––––––––––––––––––––––––––––––– About Pagoda Technologies IT services Pagoda Technologies is a globally recognized IT support company doing business in Santa Cruz, San Jose and all over the world and who is working to help businesses and their IT departments run smoothly and efficiently. To learn how Pagoda Technologies can help your business, email us at support@pagoda-tech.com to schedule a no cost business assessment.
|
Return to Pagoda Blog Main Page |